TU’s College of Engineering and Computer Science welcomes students from around the world to experience TU’s elite educational experience in the sciences, engineering and technological fields. We combine the development of creativity and ingenuity with foundational learning to prepare graduates for successful, enduring careers in domestic and international markets.
College of Engineering & Computer Science
85% Faculty Hold Highest Degree in Field
14:1 Student-Faculty Ratio
91% Placement Rate Within 6 Months
1,833 Engineering & Computer Science Students
Explore Programs
Start your career
About the College of Engineering & Computer Science
The mission of the College of Engineering and Computer Science is to provide a modern, high-quality educational experience for all students. We provide the knowledge and principles upon which engineering and science are founded in order to graduate engineers and scientists who are technically competent, creative, literate, ethically informed and socially aware.
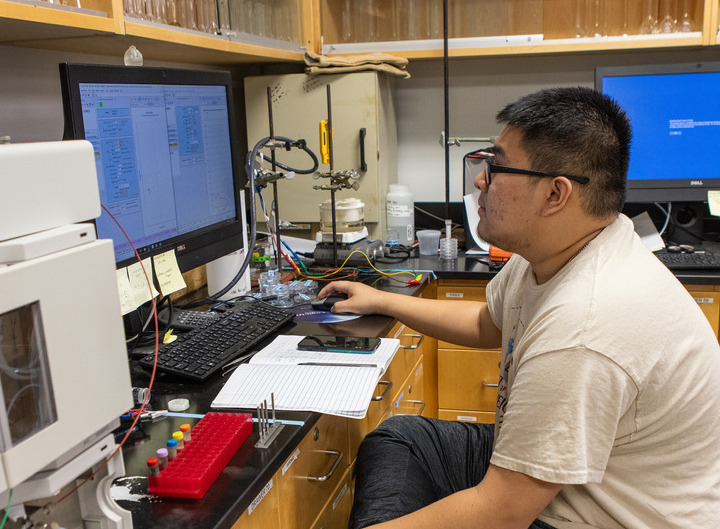
From the classroom to a career
More than 90 percent of alumni from the College of Engineering & Computer Science obtain employment or begin graduate school within six months of graduation. Whether your goal is to protect cyber space at Google or design electric vehicles for Ford, TU can make your dreams a reality.